 |
|
Users
| |
Enumeration
nmap
| |
Foothold
intelligence.htb
On découvre un site web sur le port 80 de notre machine.
Fuzzing files
Sur la page d’accueil on nous indique un lien vers un fichier :
http://intelligence.htb/documents/2020-01-01-upload.pdf Un deuxième lien est présent avec un fichier contenant une autre date.
On fait la déduction que d’autres files peuvent etre présents, si l’on réussi à faire du fuzzing avec la date.
Dans un premier temps, on génére donc un fichier Python qui parcourt toutes les dates dans le bon format de 2015 à 2022 pour un premier test. On redirige ensuite la liste dans un fichier.
| |
Ensuite, on utilise ffuf pour faire du fuzzing et récupérer toutes les URL des potentiels fichiers téléchargeables :
| |
Il faut ensuite parcourir cette liste d’url pour télécharger tous les fichiers. En Python, ça nous donne le code suivant :
| |
Dans le dossier pdfs/ se trouve une grande quantité de fichiers
Password found in pdfs
J’ai utilisé la commande pdftotext afin de convertir les pdfs en texte. Ensuite, en affichant le texte de tous les pdfs et en recherchant le mot clé “password”, on trouve un match ! Le mot de passe : NewIntelligenceCorpUser9876
| |
On trouve également le message suivant:
| |
User list from pdfs creators
En utilisant exiftool, on peut recuperer beaucoup d’information sur les PDFs et notamment le nom des createurs ayant généré les pdfs. On peut alors obtenir une liste d’utilisateurs potentiels
| |
Avec kerbrute, on peut vérifier si les utilisateurs existent. Une très grosse partie existe en vérité. Avec nxc on effectue un password spray et on trouve les credentials suivants:
intelligence.htb\Tiffany.Molina:NewIntelligenceCorpUser9876
| |
Tiffany.Molina : user flag
On trouve un Share User accessible en lecture par Tiffany. On trouve finalement les fichiers de Tiffany et le flag user.txt
| |
Rusthound bloodhound
| |
Tiffany.Molina -> Ted.Graves
SMB : IT Share
En se connectant au share IT on remarque un script powershell. Ce script parcourt tous les domaines DNS enregistrés commencant par “web” puis effectue une requête HTTP avec Invoke-WebRequest. Si le site n’est pas actif, alors la requête echoue et un mail est envoyé à Ted.
Il est indiqué que le script est executé toutes les 5mn, et vraisembablement est executé par Ted lui même. On remarque l’utilisation du paramètre -UseDefaultCredentials ce qui signifie que les creds de celui qui l’execute sont transmis lors de la requête.
Si on arrive à detourner le script pour lui faire faire une requête vers notre ordinateur, on pourrait recupérer le mot de passe de Ted.
| |
L’idée est donc:
- Créer un record DNS commençant par “web” avec le compte de Tiffany
- Mettre en place un responder, qui attend de recevoir une requête et nous donnera un hachage
- Déchiffrer le hachage.
New DNS Record
On crée un nouveau DNS record : web666. Il pointe vers notre IP. Pour cela on peut utiliser l’outil dnstool.py :
| |
Responder
On se met en attente d’une requête, avec la commande responder :
| |
Ted NTLMv2 Hash
On effectue une attaque par dictionnaire sur le hachage NTLMv2 de Ted.graves et on obtient les credentials suivants :
Ted : Mr.Teddy
| |
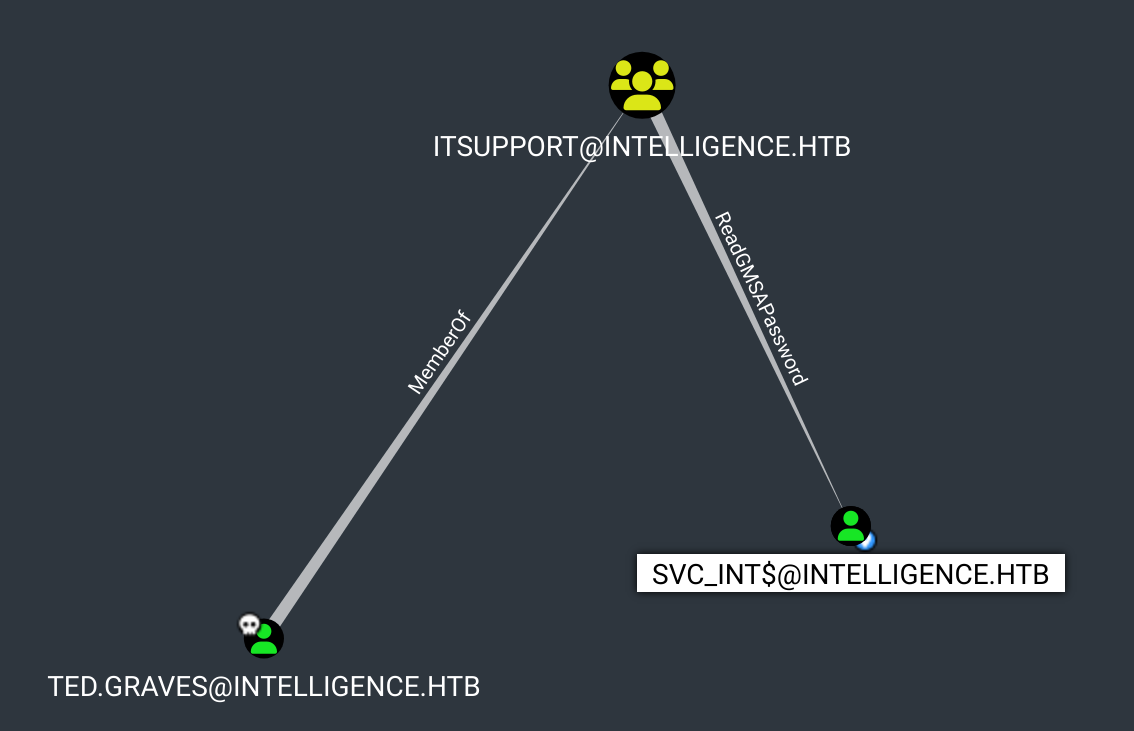
Ted.Graves -> svc_int$
ReadGMSAPassword Right on svc_int$
En utilisant bloodhound, on découvre que Ted.Graves fait parti du groupe ITSupport qui a le droit ReadGMSAPassword sur l’utilisateur svc_int$.
En utilisant la commande gMSADumper.py on peut alors dumper le hachage de svc_int$ :
| |
svc_int$ -> Administrator
msDS-AllowedToDelegateTo : WWW/dc.intelligence.htb
On remarque que svc_int peut : msDS-AllowedToDelegateTo : WWW/dc.intelligence.htb
Ce qui veut dire que svc_int$ peut se faire passer pour un autre utilisateur uniquement vers le service WWW/dc.intelligence.htb. On peut aussi voir ce resultat directement dans bloodhound.
| |
Silver Ticket : impersonate Administrator
On peut maintenant se faire passer pour l’administrateur en générant un silver ticket pour le SPN WWW/dc.intelligence.htb.
On utilise ensuite psexec pour obtenir un powershell en tant qu’admin avec le ticket généré :
| |
Tips
Parfois bloodhound n’affiche pas toutes les informations. Par exemple, je ne voyais pas la route de Ted vers svc_int.
En effet, j’ai l’habitude de cliquer sur Outbound Object Control-> Transitive Object Control.
Mais il fallait faire :
- Outbound Object Control -> Group Delegated Object Control
Attention donc à bien regarder toutes les possibilités de Outbound Object Control sur un utilisateur owned.
Allowed To Delegate : WWW/dc.intelligence.htb Il faut regarder chaque parametre de l’utilisateur sur bloodhound. J’aurais dû reperer cela. Tout ne saute pas forcement aux yeux.
psexec.py -k -no-pass intelligence.htb/Administrator@dc.intelligence.htb Pour psexec, attention ici j’ai du préciciser Administrator@dc.intelligence.htb au lieu de l’ip que j’avais mis initialement : Administrator@10.10.10.248. Il faut bien sûr que **dc.intelligence.htb **soit bien dans le /etc/hosts.